 REFOG Keylogger
REFOG Keylogger
Exploring the Capabilities of REFOG Keylogger: An In Depth Review
In today's digital age, the threat of unauthorized access to personal and sensitive information is a significant concern for both individuals and businesses. Among these threats is the presence of keyloggers, which are malicious programs designed to capture every keystroke on your computer, including sensitive data like passwords. Such software poses a serious risk, potentially leading to identity theft and financial fraud. To safeguard against these threats, implementing a robust monitoring solution like REFOG Keylogger is essential.
REFOG Keylogger offers a seamless and stealthy way to monitor computer activity, ensuring that unauthorized installations of harmful software are effectively prevented. Unlike other keyloggers that might be visible or require complex activation procedures, REFOG Keylogger operates discreetly, making it nearly impossible for even tech savvy users to detect or disable.
Seamless Monitoring and Invisible Operation
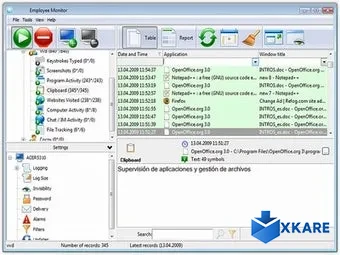
The standout feature of REFOG Keylogger is its ability to track all computer activities with ease. The software leverages a unique connection link that only the computer's owner can access. This link can integrate directly with the Windows registry or be identified through an internet connection. Once established, REFOG Keylogger captures every keystroke and screen action in real time.
- Invisible Mode: Operates stealthily, without displaying any icons or alerts, ensuring it remains undetected.
- User Friendly Interface: Unlike other software that demands usernames and passwords for activation, it employs an accessible program called EasyUninstaller for seamless operation.
Data Logging and Secure Storage
After establishing the connection, REFOG Keylogger not only logs keyboard inputs but also records on screen activities. This data is then securely transmitted to an online account, where it is stored for future reference, offering a comprehensive log for monitoring purposes.
In conclusion, embracing a solution like REFOG Keylogger is crucial for anyone looking to protect their digital world from unauthorized access and potential data breaches. Its ability to function invisibly and log data effectively makes it a reliable tool for monitoring computer activities without compromising user awareness or security.
Download Now
Technical
| Title | REFOG Keylogger |
|---|---|
| Language | German, English, Spanish |
| License | Trial version |
| Author | REFOG |
| Filename |
